“A house, divided against itself, cannot stand.” -- A Lincoln
IT Operations personnel, and software/hardware vendors have an ethical duty to protect our employer, and our users and take responsibility for network vulnerability management. It’s a duty we take seriously, and one made harder by bad actors working for the various security services around the world. Recently, and to their credit, Juniper publicly and bluntly announced a vulnerability found in Screen OS. Unlike other vulnerabilities this one wasn’t an accident, it was created, and added by a bad actor. It’s likely this bad actor works, or worked for a nation state.
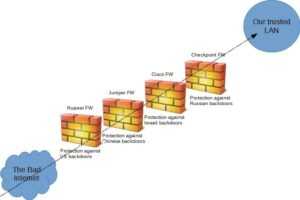
Because of Edward Snowden’s many disclosures, we now know that our shared ethical responsibility to protect our employer, and users is directly at odds with the goals of “cyberwar” obsessed intelligence services. One might also reasonably imagine then that other security products are in no better a state. Anti-virus, LDAP, server firmware, encryption hardware have to be considered suspect. This means that we cannot trust our own hardware, or software anymore. We’re fundamentally unable to fulfill that responsibility through technology.
What does this new reality mean for Vendors, and IT Operation, especially those who do security analysis? If you work for a software/hardware vendor, “if you see something, say something”. Get ahold of your boss, and your security team if something doesn’t look right. If you’re an end user of these products, or a purchaser, you need to ask about their code review process. How often is the code reviewed, who reviews it, and can you get the report from the last review? If they don’t review their code base, and won’t tell you what they found, it’s past time to look elsewhere.
Who is Safe From Government created Network Vulnerability?
The answer to this should be obvious. Open Source software! Because Open Source code is developed, committed, tested, and released in the eyes of the public, it is very difficult for a government actor to insert vulnerable code into Open Source security products. At the beginning we said you couldn’t trust Antivirus software, but there’s ClamAV! We said you couldn’t trust commercial LDAP implementations, so use OpenLDAP! We said you couldn’t trust hardware based encryption, and the good news is GPG and GNUTLS are both secure, and auditable.
Server and Network Hardware firmware is still hard to audit. As embedded systems continue to develop, alternatives for many of these products are becoming available using off the shelf hardware. Linux itself has a complete high performance firewall system built directly into the kernel, and PPTP/IPSEC implementations which are open and well tested. Until we can trust the firmware coming from proprietary vendors, Open Source will fill the gap with trustworthy code.
Interested in learning more? Enter your email address below to subscribe to our blog!